Author Archives: Jesper Udby
Salesforce wsc: upsert null fields
The salesforce upsert() call is brilliant for interfacing legacy systems with Salesforce, especially if the data you are going to replicate into already contains some sort of unique identification. It will create records that does not exist, and update … Continue reading
Salesforce wsc: ConnectionException should have been Fault
This is the first article where I discuss details or issues using wsc (JAVA) on an Oracle WebLogic platform to integrate Customer Legacy systems with Salesforce CRM. In some environments (specifically the WLS 10.3.5 used as production environment at my … Continue reading
usl4j – Ultra Simple Logging for JAVA
Back in the late 90’ties when I started programming JAVA there were no standard way of logging in JAVA programs. One usually just used System.out.println(), System.err.println() and Exception.printStacktrace(). Often applications would build homemade logging frameworks that would also log information … Continue reading
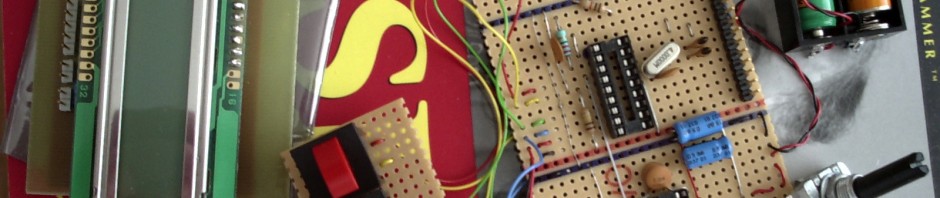
Simple logarithm implementation in PIC assembler
Most natural observations are exponentational/logarithmic in nature. I often do simple hardware using Microchip PIC processors (usually 12F or 16F families). Hardware doing some business in the home. One such example is my Christmas-tree-lightning-controller. Basically it only turns my electric … Continue reading
Locking a row, portable between databases, with JDBC
A couple of years ago I was with a project designing a system to manage Investor Meetings. An Investor must have a valid Pass in order to join a Meeting. Each Pass has a unique serial number. It was a … Continue reading
Squareroot (sqrt) with BigDecimal
Recently I was refactoring some code from using double to using BigDecimal and suddenly needed a square root method. I remembered years ago I was taught a simple “successive approximation” method; believe it was grammar school. I searched the net … Continue reading
Implementing a simple database semaphore
In this article I will describe a simple technique that enables you to implement an “exclusive lock” in a distributed, even clustered, environment. The technique works with all major databases, and should work with any database that has a reasonable … Continue reading
Financial (monetary) computations using floating point arithmetic [in JAVA]
In this article, I will discuss some of the issues in doing financial calculations in JAVA. The issues are not related to JAVA only, but to any calculation done in a “computer language” using binary floating point arithmetic, including calculations … Continue reading
Securing J[2]EE applications, part 3
In this third article, the samples are modified to be run on JBoss (4.0.3+) and JavaDB (Derby version 10.2). The first article showed how to setup Glassfish authentication with only a single database table. The second article evovled the simple … Continue reading
Securing J[2]EE applications, part 2
The first part, Securing J[2]EE applications, part 1, discusses a simple setup where a single database table, 2 views and a correctly configured jdbcRealm could handle the most basic authentication and authorization requirements. This second article discusses a few enhancements … Continue reading